The Joint Cyberspace Command offers recommendations to combat Denial of Service cyber-attacks
The aim of criminals is to blackmail victims financially, and it is advisable to limit the use of public WiFi networks, as well as the use of antivirus software, among other measures.
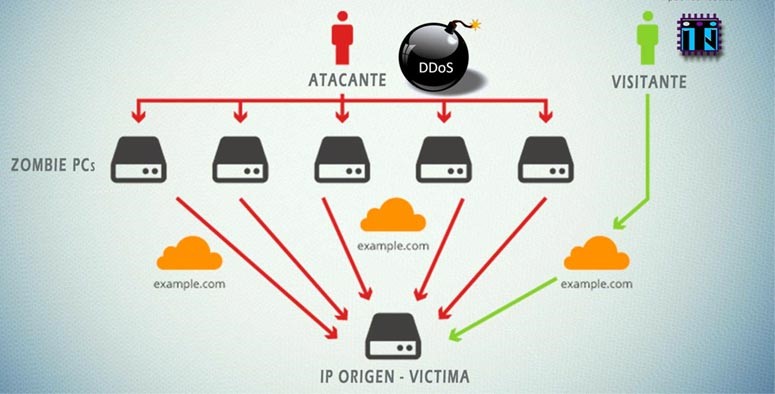
The Joint Cyberspace Command has warned about Distributed Denial of Service (DDoS) attacks, which involve overloading computer servers by sending a high volume of malicious messages from multiple sources. This drains system resources and causes poor performance or even service downtime. With these attacks, cybercriminals aim to use economic blackmail and demand ransom money from victims.
Thus, the Joint Cyberspace Command recommends the use of a number of tools and procedures. The first step is to make use of DDoS mitigation servers and configure advanced firewalls to block malicious requests before they can reach the server. It is also advisable to use Intrusion Detection Systems (IDS) or IPS, which help detect DDoS attack patterns in real time.
In addition, to avoid falling into botnets and being part of a DDoS attack without being aware of it, we should limit the use of public WiFi networks and check unknown programme files with our antivirus. If you have detected this threat or suspect that you may be part of a botnet, in Spain you can contact INCIBE-CERT and its 017 helpline.
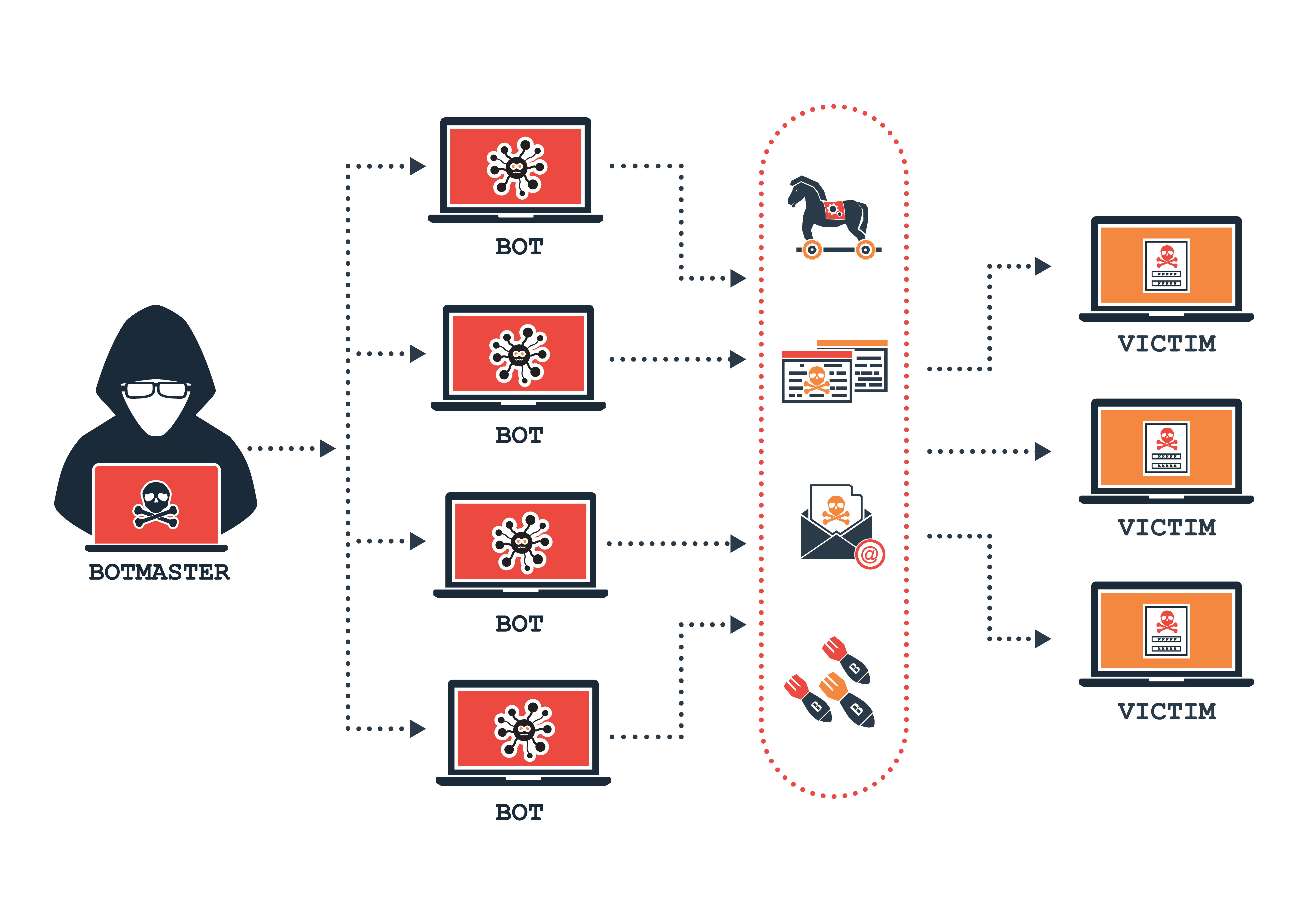
DDoS attacks base their effectiveness on the instrumentalisation of users accessing the attacked service with their devices. Between 70% and 90% of those who participate in a botnet, that is to say, a malware-infected network, do not know that they are part of it. Therefore, DDoS attacks are used by making use of infected devices controlled by a person or group carrying out the attack.
Devices are usually infected through computer worms that spread across computers on the same network. There are three main types of DDoS attacks active on networks:
· Volumetric attacks: The most common using a series of botnets together. They seek to flood unwanted traffic with the aim of saturating the bandwidth of the attacked network, blocking legitimate traffic and disrupting the operation of the service.
· Protocol attacks: They use a type of attack based on requests, for example, slowing down the contact between a web page and the server, which are not completed, causing the server to store resources unnecessarily. This storage, multiplied by several orders of magnitude, can lead to a server crash. These attacks are carried out using legitimate IP addresses obtained from the aforementioned botnets, which increases the difficulty of detection.
· Application attacks: These consist of attacking components of an application or web page by imitating the behaviour of a real user. These attacks focus on specific processes and do not require large numbers, unlike volumetric attacks. These attacks are particularly effective when attacking both the network and the server.
Cybercriminals aim to blackmail the victim financially by demanding monetary ransom. Typically, these extortions force the user to make their payments through the use of cryptocurrencies and through the Deep Web, with all the risks that this entails. Their services are often hired by third parties for the purpose of corporate espionage, sabotage and theft of personal data.
Fotos